What NVIDIA’s NemoClaw Means for Enterprise Autonomous Agent Development
What NemoClaw Actually Is (And What It Isn’t)

NemoClaw is NVIDIA’s open-source enterprise security wrapper for OpenClaw. It installs in a single command on top of an existing OpenClaw setup and adds three things: a sandboxed execution environment, a policy engine, and a privacy router. It’s licensed under Apache 2.0, runs on any hardware, and is currently in alpha preview.
Let’s be specific about what NemoClaw is not: it is not a fork of OpenClaw, not a replacement, and not a standalone product. It’s a security layer that wraps around OpenClaw. Existing OpenClaw configurations work inside NemoClaw without code changes.
NVIDIA announced NemoClaw on March 17, 2026, at GTC. Jensen Huang framed it simply: “For the CEOs, the question is, what’s your OpenClaw strategy?” OpenClaw has become the default operating system for autonomous AI agents, and now NVIDIA wants to make it enterprise-ready.
Peter Steinberger, OpenClaw’s creator, put it this way: “With NVIDIA and the broader ecosystem, we’re building the claws and guardrails that let anyone create powerful, secure AI assistants.”
Why Enterprise Agent Security Matters Now
Chatbots answer questions. Agents do work. That distinction changes the security model completely.
An autonomous agent has persistent shell access, credential management, and the ability to spawn sub-agents. That’s a fundamentally different threat surface than a chatbot generating text responses. The agent can read files, execute code, make API calls, move money, and modify systems. If it’s compromised through prompt injection, a supply-chain vulnerability, or simply a bad decision in its reasoning chain, the blast radius is real. And unlike a chatbot, where the worst case is a bad answer, a compromised agent can take actions that are difficult or impossible to reverse.
NVIDIA frames this as the “safety-capability-autonomy” trilemma: with existing approaches, you can reliably get two of the three, and the third suffers. Want a highly capable, highly autonomous agent? Security gets hard. Want a secure, autonomous agent? You limit what it can do. Want a secure, capable agent? You need a human approving every action, which defeats the point of autonomy.
We see this daily. We run a team of autonomous agents at Fountain City. These agents operate on scheduled cron jobs, read and write files, make API calls to WordPress, and coordinate through structured handoffs. The security questions are practical and daily: what can each agent access, what happens when one makes a bad API call, how do we audit what they did at 3 AM.
The current approach for most organizations, including ours, is defense in depth: scoped agent permissions, network restrictions, approval workflows for sensitive operations, and regular auditing of agent behavior. It works, but it’s a discipline-dependent system. Every new agent, every new tool integration, every new capability requires a human to think through the security implications and implement the right constraints. That doesn’t scale well, and it’s exactly the gap NemoClaw is designed to fill.
A Gartner report from December 2025 identified governance platforms for AI agents as crucial infrastructure for enterprise adoption. PYMNTS research shows 7% of U.S. enterprise CFOs have already deployed AI agents in live finance workflows, with another 5% running pilots. The demand is real. The governance tooling has been lagging behind.
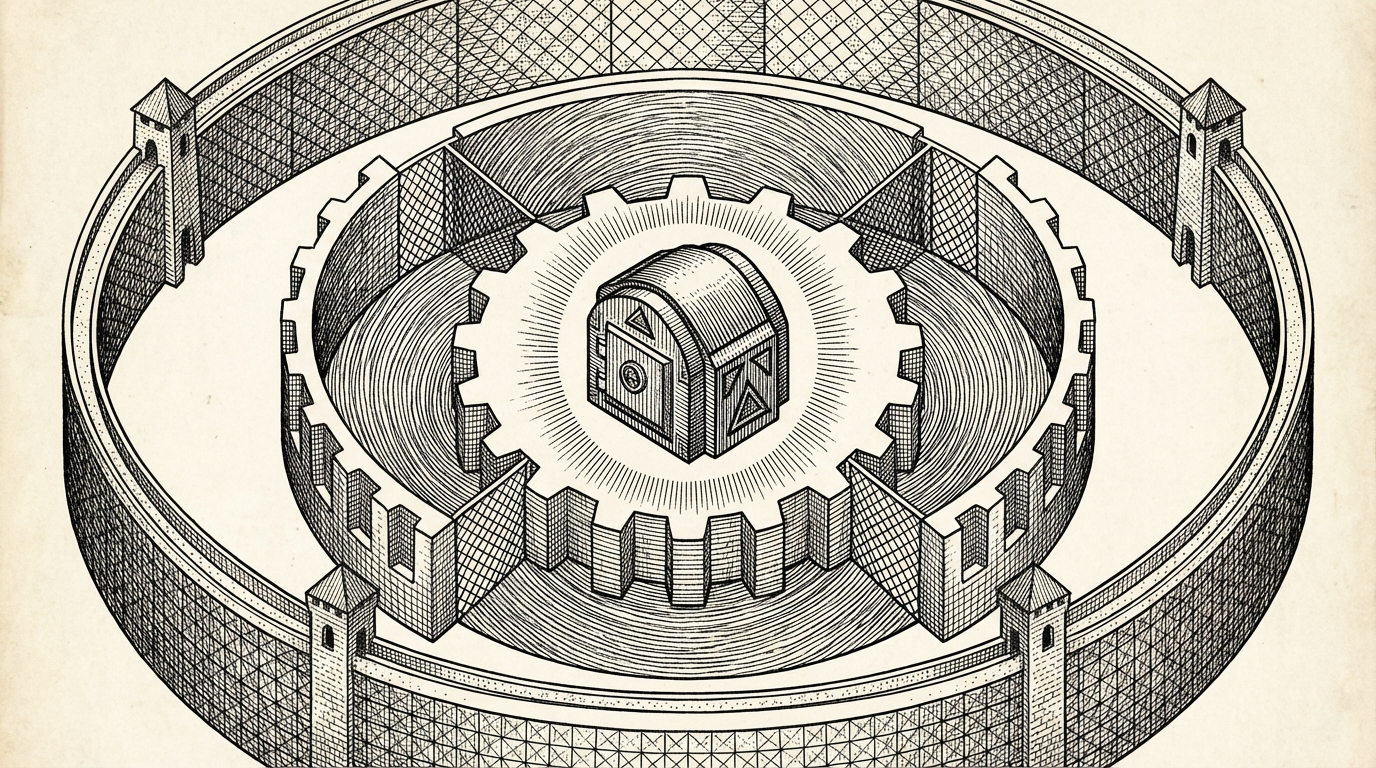
How NemoClaw Works: A Practitioner’s Breakdown
NemoClaw’s security architecture runs through a runtime called OpenShell. It has three components, and each addresses a specific category of risk. Understanding these at an architectural level matters because the design decisions here are what separate NemoClaw from lighter-weight alternatives. OpenShell is compatible with Claude Code, Cursor, Codex, OpenCode, and other coding agents in addition to general-purpose OpenClaw agents.
The Sandbox
OpenShell creates isolated execution environments for agents. Every agent runs in its own sandbox with deny-by-default permissions. The sandbox supports live policy updates, so you can tighten or loosen constraints without restarting the agent. Every action gets logged to an audit trail.
The practical implication: if an agent is compromised through prompt injection or a supply-chain attack, the blast radius is contained to that sandbox. It cannot reach other agents, other file systems, or other network endpoints unless policy explicitly allows it.
The install command tells the story of how this works in practice:
openshell sandbox create --remote spark --from openclaw.
One command creates an isolated environment, pulls in the OpenClaw runtime, and applies the default security policy. From the agent’s perspective, nothing changes. From the infrastructure perspective, everything the agent does now runs inside a controlled boundary.
The Policy Engine
Policy enforcement runs out-of-process. The constraints exist outside the agent’s reach. The policy engine enforces rules at the filesystem, network, and process level. It can approve or deny individual binaries. It handles skill verification, meaning an agent can only use tools and capabilities that have been explicitly whitelisted.
Even if the agent is fully compromised, it cannot override or modify its own policy boundaries. This is a meaningful departure from most current approaches, where guardrails are implemented as part of the agent’s own prompt or code.
The Privacy Router
The privacy router controls which data goes where. Sensitive information can be processed by local models running on-premise, while less sensitive tasks get routed to frontier cloud models. The routing decisions are policy-driven, so an organization can enforce data residency rules at the infrastructure level rather than relying on developers to make the right call in code.
This matters for regulated industries. A healthcare company using autonomous agents needs to know that patient data never leaves their infrastructure, even when the agent is calling an external API for a related task. The privacy router makes that a policy enforcement question, not a code review question.
It also addresses cost. Local models running on-premise hardware have different cost profiles than cloud API calls. The privacy router gives organizations a mechanism to route tasks based on both privacy requirements and cost policy, which becomes significant at scale when agents are making hundreds of model calls per day.
NemoClaw in Context: The Enterprise Agent Platform Landscape
NemoClaw isn’t the only answer to enterprise agent governance. The space is moving fast, and no clear winner has emerged. Here’s where the main approaches stand.
| Platform | Type | Open Source | Models | Security Model | Maturity |
|---|---|---|---|---|---|
| NemoClaw (NVIDIA) | Security wrapper for OpenClaw | Yes (Apache 2.0) | Any (model-agnostic) | Out-of-process sandbox + policy engine + privacy router | Alpha preview |
| OpenAI Frontier | Enterprise agent management | No (closed) | OpenAI models only | Integrated platform governance | GA (Feb 2026) |
| LangChain / LangSmith | Framework + observability | Yes | Any | Advisory (tracing, evaluation) — not enforced | Production |
| NanoClaw / DIY | Docker-based sandboxing | Yes | Any | Container isolation only — no policy engine | Production (limited) |
| CrowdStrike / Cisco | Security vendor integrations | No | Varies | Agent governance via existing security platforms | Early stage |
NemoClaw (NVIDIA): Open-source security wrapper for OpenClaw. Three-component architecture (sandbox, policy engine, privacy router). Hardware agnostic. Apache 2.0. Currently alpha. Built in collaboration with CrowdStrike, Cisco, and Microsoft Security. Strength: deep, out-of-process security for OpenClaw specifically. Limitation: only works with OpenClaw-based agents.
OpenAI Frontier: Enterprise agent management platform launched February 2026. Closed ecosystem tied to OpenAI models. Handles deployment, monitoring, and governance for OpenAI-native agents. Strength: tight integration with GPT models, polished enterprise tooling from a company with deep deployment experience. Limitation: vendor lock-in. If you want to use Claude for some tasks and GPT for others, or switch models as pricing and capabilities shift, Frontier constrains those choices. For organizations committed to the OpenAI ecosystem, it’s a strong option. For everyone else, the lock-in is a real trade-off.
LangChain/LangSmith: Framework-level tooling focused on observability, tracing, and evaluation. Less about hard security enforcement, more about visibility into what agents are doing. Strength: broad model and framework support. Limitation: governance is advisory, not enforced at the infrastructure level. LangChain is a launch partner for NemoClaw’s Agent Toolkit and OpenShell integration.
NanoClaw/DIY Sandboxing: Lighter-weight alternatives using Docker-based isolation. Good for development and testing. Strength: simple, low overhead. Limitation: no policy engine, no privacy routing, no audit trail. Fine for prototyping, insufficient for enterprise production.
CrowdStrike/Cisco Integrations: Enterprise security vendors adding agent governance capabilities to their existing platforms. Strength: integrates with existing security infrastructure. Limitation: early stage, capabilities still being defined. Both are NemoClaw launch partners, suggesting convergence rather than competition.
NemoClaw is the most comprehensive open-source option for organizations already using OpenClaw. If you’re not on OpenClaw, or if you need multi-framework governance, the landscape is still fragmented. The convergence between NemoClaw and enterprise security vendors (CrowdStrike, Cisco) suggests that agent governance may eventually integrate into existing security infrastructure rather than remaining a standalone concern. That would change the evaluation calculus significantly.
What We Still Don’t Know
The gaps in publicly available information are significant for anyone making infrastructure decisions.
Will NemoClaw become the standard, or will the space fragment? NVIDIA has the ecosystem weight to push NemoClaw toward default status for OpenClaw users. The CrowdStrike, Cisco, and Microsoft Security partnerships suggest serious enterprise intent. That said, OpenAI’s Frontier platform, Google’s agent governance work, and emerging open-source alternatives could create a fragmented market where organizations need multiple governance layers. We don’t know yet.
How does the alpha perform in production? NVIDIA themselves describe NemoClaw as early-stage. “Expect rough edges” is the direct language. Nobody outside NVIDIA and a handful of launch partners has run NemoClaw in a real production environment. Performance benchmarks, failure modes, and operational quirks are all unknowns.
What’s the performance overhead? Sandboxing and policy enforcement add latency. For agents doing quick text generation, this might be negligible. For agents running complex multi-step workflows with dozens of tool calls, the cumulative overhead could matter. No published benchmarks exist yet.
Does “hardware agnostic” hold up in practice? NemoClaw officially runs on RTX PCs, DGX Station, DGX Spark, cloud, and on-premise infrastructure. Whether the experience is equally good across all of these, or whether NVIDIA hardware gets quiet optimization advantages, remains to be seen.
How do policy updates work with fast-moving agent codebases? Agents evolve quickly. New tools, new capabilities, new integrations. The policy engine needs to keep pace. How that works operationally, whether it’s a manual process or something that can be automated, will determine whether NemoClaw scales gracefully or becomes a bottleneck.
There’s also the question of multi-agent coordination. NemoClaw’s documentation focuses primarily on individual agent sandboxing. Organizations running teams of agents that need to communicate with each other, pass files, share state, and trigger each other’s workflows face additional governance questions that NemoClaw’s current architecture may or may not address well. We’re watching this closely, since our own agent team relies heavily on structured inter-agent communication.
These are the questions any responsible technical leader should ask before committing infrastructure to a new platform. NemoClaw’s potential is significant, and these answers will become clearer as the alpha matures.
How to Evaluate NemoClaw for Your Organization
If you’re considering NemoClaw, five questions will help frame the decision.
1. What agent platform are you currently using? If you’re already on OpenClaw, NemoClaw is the natural next step for enterprise security. If you’re on a different framework, NemoClaw doesn’t apply directly, and you’ll need to evaluate alternatives or consider migration.
2. What are your data residency requirements? The privacy router is NemoClaw’s most distinctive feature for regulated industries. If you need to enforce where sensitive data gets processed, at the infrastructure level rather than in application code, NemoClaw addresses that directly. If data residency isn’t a concern, this feature matters less.
3. What’s your current security posture for AI tools? Organizations already running agents with ad-hoc security (manual permission management, code-level guardrails, Docker isolation) have the most to gain from NemoClaw’s structured approach. Organizations that haven’t deployed agents yet might want to evaluate NemoClaw as part of their initial architecture rather than retrofitting it later.
4. How fast is your agent codebase evolving? NemoClaw’s live policy updates are designed for fast-moving environments. If your agents are stable and rarely change, static security configurations might be sufficient. If you’re iterating quickly, adding new tools and capabilities weekly, the dynamic policy engine becomes more valuable.
5. What’s your timeline? NemoClaw is alpha. If you need production-grade agent security today, you’ll need to build interim solutions while NemoClaw matures. If you’re in the experimentation or planning phase, starting with NemoClaw now lets you build security into your architecture from the beginning rather than retrofitting it later, which is always more expensive and disruptive. Consider using AI workflows and automation services to assess where agents fit in your operations before committing to a governance platform.
A sixth question, often overlooked: what’s your model strategy? Organizations using multiple model providers (Claude for reasoning, GPT for certain tasks, local models for sensitive data) benefit more from NemoClaw’s model-agnostic architecture and privacy router than organizations committed to a single provider. If you’re already all-in on one model vendor, that vendor’s native governance tooling may be simpler to deploy even if it’s less flexible.
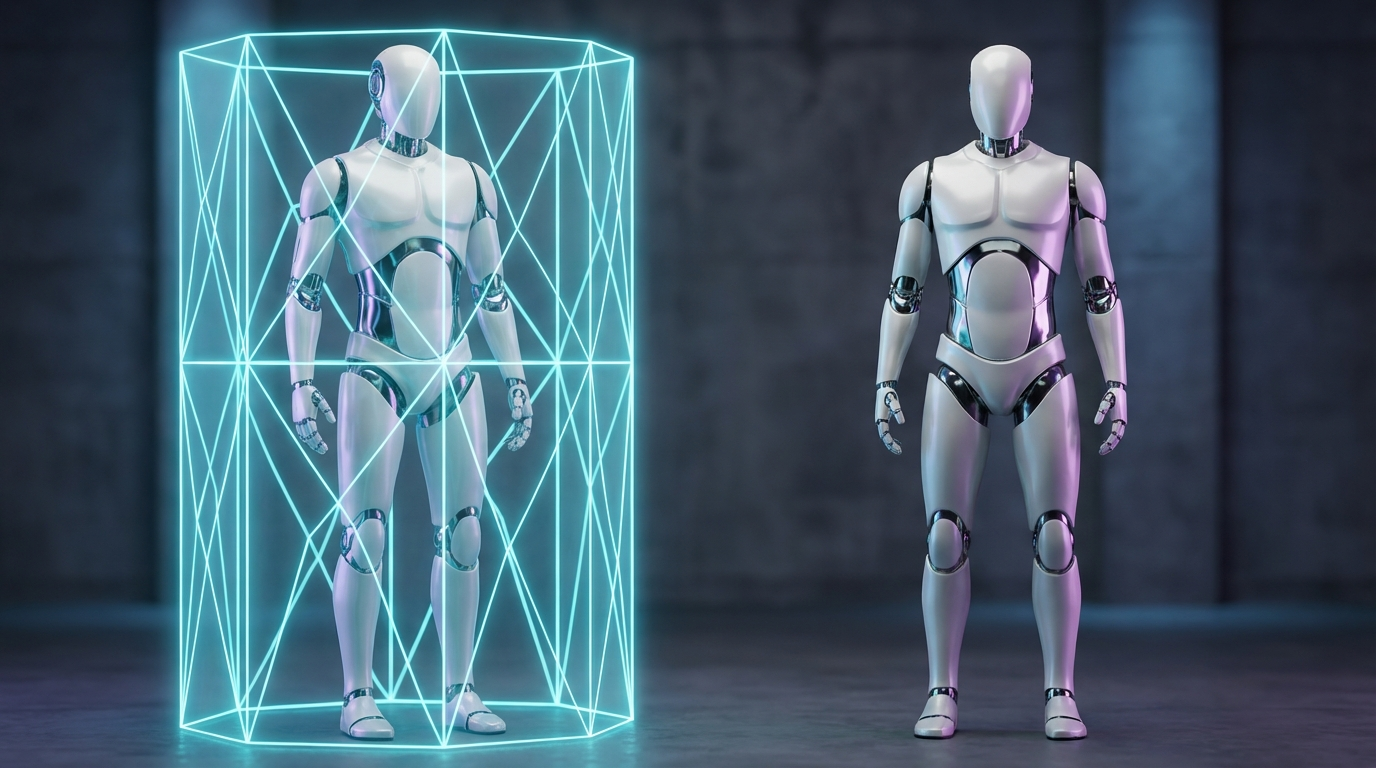
Our Perspective: What This Means for Agent Builders
We have a specific vantage point on NemoClaw because we run OpenClaw in production every day. Our AI agent teams in business operations include Scott (an autonomous SEO research agent producing 40+ content briefs per month), Aria (content writing and publishing), Kai (conversion rate optimization), and Daisy (social media distribution). These agents run scheduled workflows, access APIs, and coordinate with each other through structured file handoffs.
Security has been a practical concern from day one. Agent permissions are scoped, infrastructure is locked down, and we audit what each agent does. The practices we’ve developed through operating a production agent team are exactly the kind of thing NemoClaw aims to formalize at the infrastructure level.
The out-of-process policy enforcement is the most significant design decision in NemoClaw. Right now, agent security is largely a discipline problem. Developers need to remember to scope permissions, write proper guardrails, and audit regularly. NemoClaw moves that from discipline to infrastructure, which is how security should work.
The alpha status is the constraint. We’re watching NemoClaw closely, but we’re not committing our production agents to it until the rough edges smooth out. We’ve learned from experience that early adoption of agent infrastructure carries real operational risk.
For our clients building managed autonomous AI agents, NemoClaw is the first serious enterprise answer to the agent security question. We expect it to become a standard part of enterprise OpenClaw deployments once it reaches production readiness. Until then, we continue building security into our agent architectures using the practices we’ve refined through operating our own team.
One practical consideration: our agents currently produce content at $2-5 per published piece including research, writing, review, and image generation. That cost efficiency depends on agents running with enough autonomy to complete multi-step workflows without human intervention at every checkpoint. Any governance layer needs to preserve that autonomy while adding security. NemoClaw’s approach of out-of-process policy enforcement, where the agent operates normally within defined boundaries, is the right architecture for this. It adds security without adding approval friction to every tool call.
NVIDIA, CrowdStrike, Cisco, and Microsoft Security are all investing in agent governance infrastructure. Kari Briski, NVIDIA’s VP of Generative AI Software, described the shift: “Claws are autonomous agents that can plan, act, and execute tasks on their own. They’ve gone from just thinking and executing on tasks to achieving entire missions.” When the security industry’s biggest names are building governance tooling for autonomous agents, the message is clear: this category of software is here to stay, and the companies that figure out governance early will have a meaningful advantage.
For organizations that haven’t started building with autonomous agents yet, NemoClaw’s announcement changes the calculus. One of the biggest objections we hear from enterprise buyers is “how do we secure this?” Until now, the honest answer was: carefully, manually, with a lot of custom work. NemoClaw gives that answer an infrastructure foundation. It doesn’t remove the need for thoughtful security design, but it provides the building blocks that were previously missing.
That shifts the conversation from “can we secure autonomous agents?” to “what’s our governance architecture?” — and that’s a more productive starting point.
FAQ
What is NemoClaw?
NemoClaw is NVIDIA’s open-source enterprise security wrapper for OpenClaw. It installs in a single command and adds three components: a sandboxed execution environment (OpenShell), a policy engine for fine-grained access control, and a privacy router for controlling where sensitive data gets processed. It’s licensed under Apache 2.0 and works on any hardware.
Is NemoClaw free?
Yes. NemoClaw is open source under the Apache 2.0 license. It runs on NVIDIA hardware (RTX PCs, DGX Station, DGX Spark) as well as non-NVIDIA cloud and on-premise infrastructure. Currently in alpha preview.
Does NemoClaw replace OpenClaw?
No. NemoClaw wraps OpenClaw with enterprise security features. Existing OpenClaw setups work unmodified inside NemoClaw’s OpenShell runtime. No code changes are required.
What’s the difference between NemoClaw and NanoClaw?
NemoClaw is NVIDIA’s full enterprise stack: OpenShell sandbox, policy engine, and privacy router. NanoClaw is a lighter Docker-based sandbox for development and testing. They serve different needs. NemoClaw targets enterprise production environments that need comprehensive security, policy enforcement, and audit trails. NanoClaw is better suited for prototyping and development workflows where full enterprise governance isn’t required.
Can NemoClaw work with models other than NVIDIA’s?
Yes. NemoClaw is model-agnostic by design. It works with Claude, GPT, Gemini, and any other coding agent or language model. The privacy router can direct sensitive tasks to local NVIDIA models while routing other tasks to any cloud provider.
Is NemoClaw production-ready?
Not yet. NemoClaw is in alpha preview as of March 2026. NVIDIA describes it as early-stage and advises users to “expect rough edges.” No production deployment benchmarks or case studies have been published outside of NVIDIA’s launch partners.
Who should consider NemoClaw?
Organizations already using OpenClaw, or planning to, that need enterprise-grade security, data privacy controls, and policy enforcement for autonomous agents. The privacy router is particularly relevant for regulated industries with data residency requirements. Organizations not on OpenClaw would need to evaluate whether migrating to OpenClaw makes sense before NemoClaw becomes relevant.